নারায়ণ আপদুদ্ধার মন্ত্র | শ্রী লক্ষ্মী-নৃসিংহ মন্ত্র | Narayana Mantra |
Disaster relief mantra
-
বিপদ থেকে উদ্ধার এবং সুরক্ষার জন্য ভগবান নারায়ণ বা বিষ্ণুর শরণাপন্ন হওয়া
সবচেয়ে শক্তিশালী উপায় বলে মনে করা হয়। শাস্ত্রে একে 'আপদুদ্ধার' মন্ত্র বলা
হয়।
...
Showing posts with the label NetworkingShow All
Email and eMail Stracture
Malin Sarkar
23:53:00
Network Topology
Malin Sarkar
10:18:00
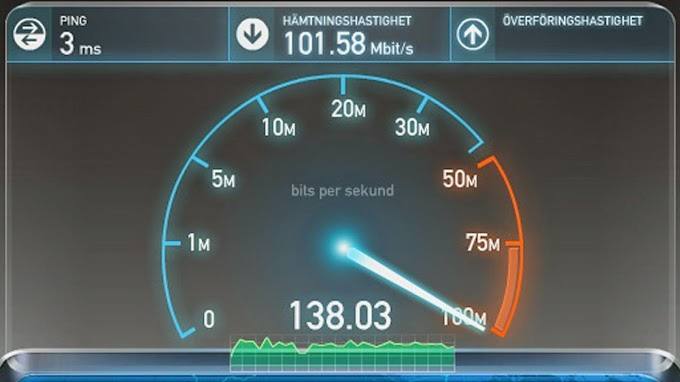
Computer Networking
Malin Sarkar
23:40:00
Popular Posts
Our Others Website
You May Like Also
Useful Links
Other's Website Content
Categories
Copyright ©
Tips Tweet- Education PC Tricks